CompTIA CAS-004 Question Answer
After a server was compromised an incident responder looks at log files to determine the attack vector that was used The incident responder reviews the web server log files from the time before an unexpected SSH session began:
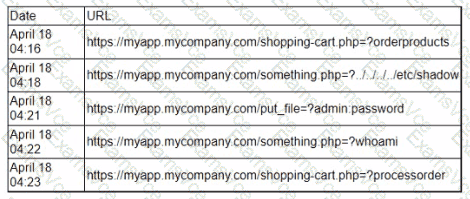
Which of the following is the most likely vulnerability that was exploited based on the log files?
CompTIA CAS-004 Summary
- Vendor: CompTIA
- Product: CAS-004
- Update on: Apr 30, 2026
- Questions: 619



