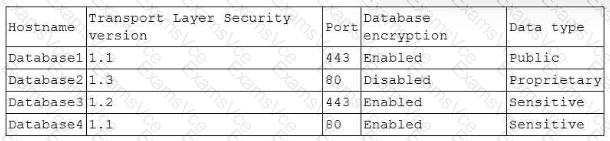
The CISO’s requirements prioritize protecting customer (sensitive) data with encryption both in transit and at rest. The database that violates the most critical requirements—especially for sensitive/customer data—should be remediated first.
Why Database4 is the highest priority
Sensitive data + no encryption in transit (Port 80): Port 80 indicates HTTP (clear-text), which means no encryption in transit. Secbay explicitly states: “HTTP is a clear-text protocol that is generally secured via an SSL/TLS tunnel to produce HTTPS transmission.”
Uses weak/unsupported TLS version (TLS 1.1) + sensitive data: Even if TLS is “listed,” TLS 1.1 is not considered acceptable in modern secure configurations. Secbay’s protocol acceptability list marks TLS 1.1 = No (not acceptable), while TLS 1.2/1.3 are acceptable.
Customer data must be encrypted in transit and at rest: Secbay provides the exact requirement-style statement: “The organization implements encryption for sensitive data both in transit and at rest… Sensitive customer data is encrypted…”
So Database4 is the most severe because it involves Sensitive (customer) data while failing the “encryption in transit” requirement (HTTP/80) and also relying on an unacceptable TLS version (1.1).
Why the other databases are lower priority
Database3: TLS 1.2 on 443 + encryption at rest enabled + sensitive data → it already meets the CISO requirements.
Database2: Port 80 (no transit encryption) and encryption at rest disabled, but the data type is proprietary, not explicitly customer/sensitive. It is still important, but Database4 is worse because it impacts sensitive/customer data.
Database1: Data type is public; while TLS 1.1 is weak, it does not violate the “customer data” requirement and is less severe than Database4’s clear-text transport for sensitive data.
References (CompTIA CySA+ CS0-003 documents / study guides used):
Secbay Press, CompTIA CySA+ Exam Prep Guide (CS0-003): encrypt sensitive customer data in transit and at rest
Secbay Press, CompTIA CySA+ Exam Prep Guide (CS0-003): HTTP is clear-text; TLS 1.1 not acceptable while TLS 1.2/1.3 are acceptable