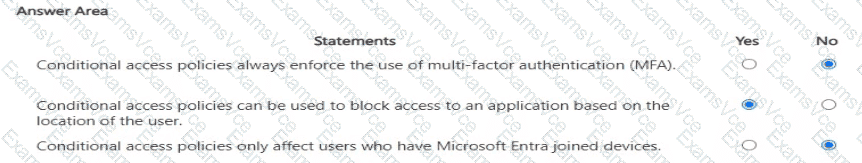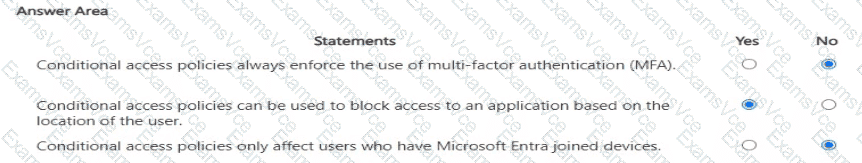
Conditional access policies always enforce MFA = NoMicrosoft Entra Conditional Access policies are flexible and do not always require MFA. MFA is one possible control, but policies can enforce other access controls such as requiring a compliant device, blocking access entirely, requiring Terms of Use acceptance, or enforcing session controls.
SCI Extract: “Conditional Access is the tool used by Azure AD to bring signals together, to make decisions, and enforce organizational policies. These policies can require MFA, but it is not mandatory for all policies.”
Block access based on location = YesConditional Access supports location-based conditions using named locations (such as country or IP ranges). Policies can block or allow access based on where the user is signing in from.
SCI Extract: “Administrators can use Conditional Access policies to block or grant access based on user location, using named locations to define trusted or risky areas.”
Only affects Entra joined devices = NoConditional Access applies to all users and devices, including:
Entra-joined,
Hybrid Entra-joined,
Registered devices (via Microsoft Intune or Azure AD),
And even unmanaged (BYOD) devices depending on configuration.
SCI Extract: “Conditional Access policies apply to all users and devices based on selected conditions, not only Microsoft Entra joined devices.”