Comprehensive and Detailed 150 to 200 words of Explanation From Exact Extract of Network Security 7.6 documents:
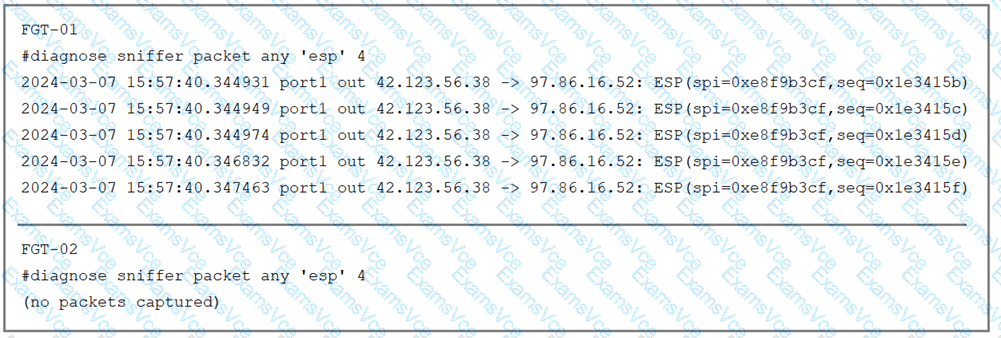
The output on FGT-01 confirms that the device is actively encapsulating traffic and sending it as ESP packets (Protocol 50) out of port1 towards the IP address 97.86.16.52. The logs show outgoing packets, which confirms FGT-01 is attempting to initiate or maintain the tunnel and that NAT-Traversal is not being used (as it uses raw ESP).
The output on FGT-02, however, displays (no packets captured). This is significant because the sniffer command diagnose sniffer packet any 'esp' captures traffic at the network interface level (ingress), regardless of whether a matching VPN configuration exists on the receiving unit. The absence of packets proves that the ESP traffic generated by FGT-01 is physically not arriving at FGT-02's interface.
This behavior is explained by two primary factors:
Option A (Blocking): An intermediate device, such as an ISP router or firewall, is dropping Protocol 50 traffic. Unlike UDP 500/4500, raw ESP is often blocked by default on many networks or legacy devices.
Option C (Routing/Misconfiguration): If the administrator configured the wrong remote peer IP on FGT-01, the packets are being routed to a different destination entirely. Consequently, they never arrive at FGT-02 to be captured.
Option B is incorrect because even without a configured VPN tunnel, the sniffer would still display the incoming ESP packets if they were reaching the interface. Option D is incorrect because FGT-01 is sending ESP, making 'esp' the correct filter.