The correct answers are C and D .
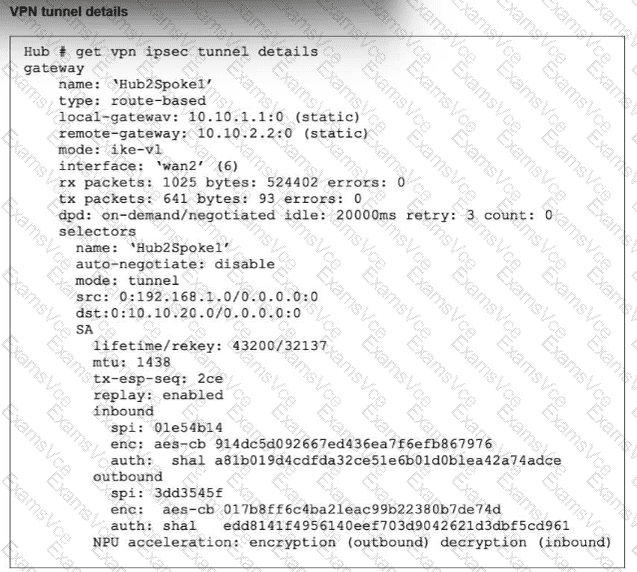
The study guide’s get vpn ipsec tunnel details example shows:
replay: enabled
inbound and outbound sections with separate SPIs
NPU acceleration: encryption(outbound) decryption(inbound) and it labels these as “Phase 2 SAs for each direction” and “Hardware acceleration”
This directly proves D. Anti-replay is enabled , because the output explicitly says replay: enabled
For the NPU status, the study guide explains the exact npu_flag meanings:
npu_flag=00 = both IPsec SAs loaded to the kernel
npu_flag=01 = outbound IPsec SA copied to NPU
npu_flag=02 = inbound IPsec SA copied to NPU
npu_flag=03 = both outbound and inbound IPsec SAs copied to NPU
Because the exhibit shows hardware acceleration in both directions — encryption(outbound) and decryption(inbound) — the matching npu_flag is 03 , not 02. That makes C correct and A incorrect.
Why B is wrong:
The same study guide output labels the tunnel as having Phase 2 SAs for each direction , so different inbound and outbound SPIs are normal for the two SAs. Also, the FortiOS administration guide explains that auto-negotiate controls whether phase 2 SA negotiation is initiated automatically, not whether inbound and outbound SPIs are different: “By default the phase 2 security association (SA) is not negotiated until a peer attempts to send data… Auto-negotiate initiates the phase 2 SA negotiation automatically…”
So the verified answers are: C, D .